Date: 22-Aug-2022
Knowledge Base vs Kn...
Large language models contain ...
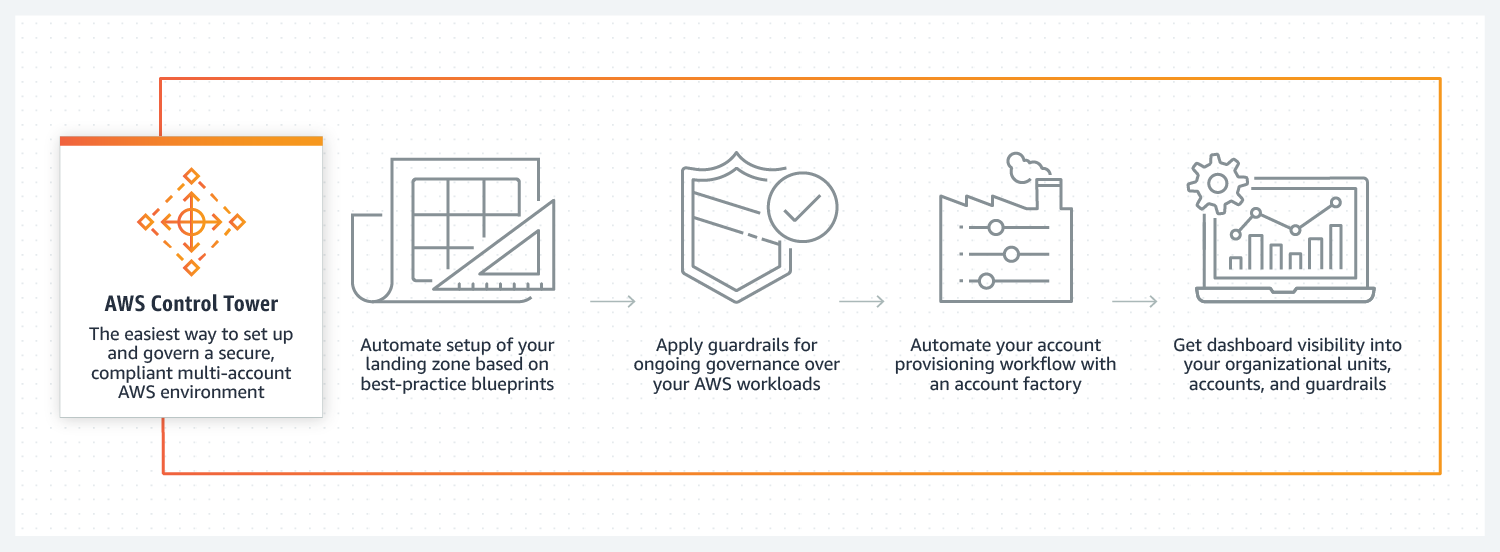
AWS Control Tower simplifies the process of setting up a new baseline for multi-account AWS environments that is secure, well-architected, and ready to use with a few clicks. This includes the configuration of AWS Organizations, centralized logging, federated access, mandatory guardrails, and networking. Control Tower is one of the best ways to start with AWS, it helps to start with built-in governance and best practices.
Source: AWS Control Tower
AWS Control Tower is based on a number of AWS services, such as AWS Organizations, AWS Identity and Access Management (IAM) (including Service Control Policies), AWS SSO, AWS Config, AWS CloudTrail, and AWS Service Catalog.
.png?width=992&name=pasted%20image%200%20(1).png)
AWS Control Tower creates accounts that provide separated environments for specialized roles in your organization as a best practice for a well-architected multi-account environment. These accounts are for management, log archival, and security auditing.
Used for billing for all accounts in an organization, creating new accounts, and managing access to all accounts
Used as a repository of logs of API activities and resource configurations from all accounts.
A restricted account for your security and compliance teams to gain read and write access to all accounts.
AWS Control Tower sets up AWS Single Sign-On (SSO) to make it easy to centrally manage access to multiple AWS accounts. Additionally, it gives users single sign-on access to all of the assigned accounts from a single location.
Guardrails are rules that provide ongoing governance for your overall AWS environment. Each guardrail enforces a single rule and is expressed in plain language.
.png?width=478&name=pasted%20image%200%20(2).png)
Guardrails have two behaviors as preventive and detective guardrails.
There are three types of guardrails.
.png?width=1600&name=pasted%20image%200%20(3).png)
Guardrail examples
Account Factory is essentially an AWS Service Catalog product which helps to automate and standardize the secure provisioning of new accounts according to defined security principles such as region selection and network configuration.
.png?width=1600&name=pasted%20image%200%20(5).png)
In the Create account section, Account and AWS SSO details can be set separately.
.png?width=1440&name=pasted%20image%200%20(4).png)
Also, Terraform can be used to provision and customize your accounts with "AWS Control Tower Account Factory for Terraform" (AFT).
AWS Control Tower is a great way to start AWS and govern multi-account AWS environments.
Building and maintaining a long-term multi-account structure is simpler with AWS Control Tower. It builds a landing zone with accounts and services needed to manage AWS environments securely and easily. AWS Control Tower helps to start with built-in governance and best practices on the cloud journey to AWS.
Mehmet is currently working as Cloud Engineer at kloia. He is mainly working on migration projects.
Large language models contain ...
While Kubernetes started its j...
The demand for GPU compute in ...
If you recently tried to invok...
As VMware licensing costs cont...